Table of Contents
- Barrier based process safety
- How do safety barriers work?
- Process risk management
- Operational discipline and risk management
- Asset integrity as a defense
- MOC, PSSR, and temporary changes
- Process Risk Metrics
- Technology to strengthen barriers
- Alarms, SIS, and Human Response
- Organizational culture and leadership
- Keys to strengthening accident prevention
- Conclusions
- References
- Frequently Asked Questions (FAQs)
A plant begins to lose control before a toxic leak, fire, or explosion occurs. The first signs are often seen in suppressed critical alarms, postponed functional tests, temporary changes that have not been closed out, expired relief valves, or barriers that no longer have verifiable evidence.
Process safety protects facilities handling flammable, toxic, or reactive substances, or hazardous energy, through barriers designed to prevent, detect, control, or mitigate major incidents. Its implementation integrates process risk, operational discipline, asset integrity, alarms, safety instrumentation, change management, and field decision-making.
Barrier based process safety
Process safety is an engineering and management discipline aimed at preventing containment failures, overpressure, fires, explosions, runaway reactions, and exposure to hazardous substances. Its application requires understanding the process, identifying credible accident sequences, defining adequate controls, and verifying that these controls remain available during normal operation, startup, shutdown, maintenance, or degraded conditions.
OSHA 29 CFR 1910. 119, Process Safety Management for Highly Hazardous Chemicals, contains requirements to prevent or minimize the consequences of catastrophic releases of toxic, reactive, flammable, or explosive substances, and includes information on process safety, hazard analysis, procedures, training, mechanical integrity, change management, pre-startup reviews, and incident investigation.
The Risk-Based Process Safety (RBPS) model, developed by the Center for Chemical Process Safety (CCPS), proposes twenty elements for designing, correcting, or improving process safety systems. Its utility lies in adjusting resources, controls, and verification levels according to the hazard, the complexity of the unit, actual exposure, and the criticality of the barriers.
How do safety barriers work?
Safety barriers are controls designed to interrupt a hazard sequence before it leads to a major consequence. They can be design-based, instrumented, mechanical, operational, administrative, or response-based.
A barrier should not be considered effective simply because it appears on a piping and instrumentation diagram (P&ID), a Layers of Protection Analysis (LOPA) matrix, or a procedure; it must demonstrate independence, reliability, availability, responsiveness, and documented testing.
In the event of a potential overpressure, the following may come into play: the basic process control, a critical alarm, operator response, a Safety Instrumented Function (SIF) within the Safety Instrumented System (SIS), a Pressure Safety Valve (PSV), and a safe venting system. If multiple layers depend on the same transmitter, an overloaded console, or modified logic without Change Management (MOC), the actual protection is weakened.
In practice, these layers can also be grouped as personnel, plant, and process controls. The first depend on competence, critical decisions, and shutdown authority; the second, on critical systems and equipment; and the third, on clear, up-to-date, and field-verifiable procedures.
Medidas preventivas y de mitigación
Preventive barriers reduce the likelihood of an incident: inherently safe design, corrosion control, operating limits, critical alarms, interlocks, work permits, power isolation, inspection, maintenance, and startup procedures.
Mitigation barriers reduce consequences through PSVs, gas and fire detection, Emergency Shutdown Systems (ESD), dikes, drains, foam, remote isolation, and emergency response. The key technical question is: Which barrier interrupts the sequence before the event reaches a major consequence?
Process risk management
Risk management begins with a precise description of the risk scenario. Simply stating “product leak” or “fire in the process area” is insufficient; it is generally necessary to identify the initiating cause, deviation, inventory involved, operating conditions, consequences, existing barriers, gaps, and actions.
Tools such as Process Hazard Analysis (PHA), Hazard and Operability Analysis (HAZOP), What-if analysis, Bow Tie, and LOPA organize this information. HAZOP identifies deviations; the Bow Tie visualizes causes, consequences, and controls; and LOPA confirms whether the independent layers of protection are sufficient. The value lies in making decisions: reducing inventory, changing design, improving detection, strengthening the SIS, updating procedures, or modifying inspection frequency.
In this sequence, HAZOP identifies scenarios and safeguards; LOPA verifies whether existing layers reduce risk to a tolerable level; and SIL defines the required reliability when risk reduction depends on an instrumented safety function.
This visual resource reinforces the relationship between HAZOP, LOPA, and SIL as a technical sequence for identifying deviations, evaluating independent layers of protection, and defining the required level of risk reduction in safety instrumented functions. Source: Oil and Gas Insights

Unlock the Secrets to Process Safety Success!
Process risk and actual exposure
Risk varies depending on the operating condition. A unit does not face the same level of exposure during steady-state operation, startup, shutdown, cleaning, maintenance, temporary bypass, or degraded operation. For this reason, it is important to distinguish between design risk, operational risk, and cumulative risk.
Cumulative risk arises when deviations coincide: a critical pump out of service, a silenced alarm, an overdue inspection, an open PHA recommendation, and an outdated procedure. Each deviation may seem tolerable on its own; together, they can leave the unit without effective protection.
Operational discipline and risk management
Operational discipline involves performing critical tasks correctly, at the required time, and within defined limits, even under pressure from production demands, maintenance delays, or urgent startup requirements. In process safety, discipline means technical adherence to operating windows, permits, procedures, alarms, interlocks, functional tests, and shutdown authority.
When a procedure requires stopping an operation under certain conditions, but daily practice allows it to continue, the organization contradicts its own protection system. Operational discipline is demonstrated in the control room, in the field, during permit reviews, rounds, shift handoffs, power lockouts, alarm responses, and the closure of deviations.
Operational errors that compromise barriers
Safety barriers are compromised by standard operating practices: persistent alarms, bypasses with no end date, outdated procedures, deferred tests, change management without documentation, startups without a complete Pre-Start Safety Review (PSSR), or expired PHA recommendations.
The technical solution is not to blame the operator. Workload, procedural clarity, training, on-site supervision, human-machine interface, alarm prioritization, availability of spare parts, and actual authority to stop an unsafe condition must be reviewed.
Asset integrity as a defense
Asset integrity serves as a physical barrier against loss of containment. Vessels, piping, tanks, valves, pumps, heat exchangers, relief systems, and critical instrumentation must maintain their mechanical and functional integrity throughout their lifecycle.
Corrosion, erosion, fatigue, vibration, incompatible materials, operation outside the specified range, or poor maintenance can turn available equipment into a source of a major incident. Therefore, inspection findings should be treated as risk information, not merely as maintenance tasks.
Inspection, RBI, and Critical Equipment
Inspection adds value when it is linked to process criticality. Risk-Based Inspection (RBI), corrosion circuits, Corrosion Monitoring Locations (CMLs) and Thickness Measurement Locations (TMLs), safety valve testing, instrument calibration, and maintenance of critical equipment must address potential consequences.
A useful practice is to classify equipment by barrier function: primary containment, relief, isolation, detection, control, mitigation, or response. Thus, maintenance and inspection prioritize based on exposure to major events, not solely on availability or the age of the work order.
MOC, PSSR, and temporary changes
Change Management (MOC) controls changes to substances, technology, equipment, alarms, control logic, materials, procedures, personnel, Operational Technology (OT) cybersecurity, and asset integrity. The U.S. Chemical Safety and Hazard Investigation Board (CSB) has indicated that a MOC methodology must be applied to both planned changes and operational deviations and variations from established conditions.
A temporary change must have an expiration date, an accountable person, a risk analysis, compensating controls, and formal closure criteria. If a bypass, a temporary line, a temporary logic, or a silenced alarm remains unreviewed, it ceases to be temporary and becomes a degraded condition.
The Pre-Startup Safety Review (PSSR) confirms that the change was installed as designed, that recommendations were closed out, that personnel were trained, and that critical barriers are in place before introducing pressure, temperature, energy, or hazardous material.
Process Risk Metrics
Measuring incidents after they occur is insufficient. API RP 754, Process Safety Indicators for the Refining and Petrochemical Industries, 3rd Edition 2021, organizes the indicators into four tiers: Tier 1 and Tier 2 track process safety events with more severe consequences and facilitate external reporting and industry benchmarking; Tier 3 and Tier 4 focus on internal monitoring of deviations, breaches of safety barriers, and preventive site management.
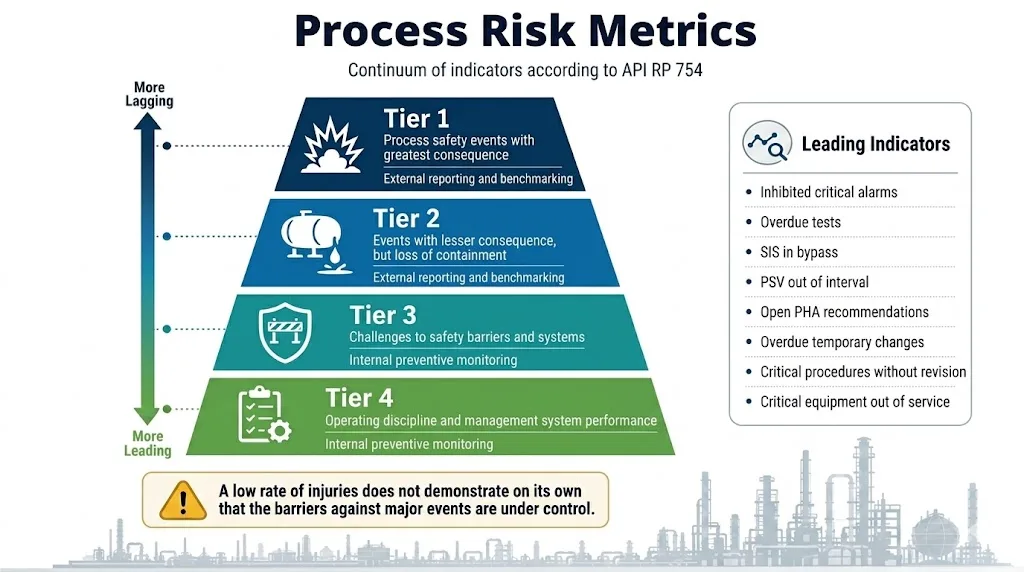
A common mistake is to assess process safety using personal safety indicators. A low injury rate does not, by itself, prove that barriers against major incidents are under control; therefore, metrics must confirm whether critical controls remain effective, reliable, and commensurate with the risk of the scenario.
Early warning indicators should signal degradation before loss of control: silenced critical alarms, overdue tests, SIS in bypass, PSVs with overdue or out-of-range tests, open PHA recommendations, overdue temporary changes, unreviewed critical procedures, permits with recurring findings, and critical equipment out of service.
Barrier health chart
| Critical barrier | How it degrades | Evidence to be reviewed | Recommended action |
|---|---|---|---|
| Critical slarms | Fatigue, poor prioritization, inhibition | Persistent alarms, chattering, slow response | Rationalization and Monitoring of ANSI/ISA-18.2 |
| SIS / SIF | Expired tests, bypass, logic change | Test records, MOC, actual demand | IEC 61511 Compliance and Bypass Control |
| Mechanical integrity | Corrosion, leak, expired inspection | CML/TML, RBI, PSV, open findings | Prioritize by barrier criticality |
| Procedures | Outdated or low adherence | Field audits, deviations | Operational verification and training |
| MOC/PSSR | Changes without a technical close | Open positions, expired trades | Formal closure before launch |
| Work permits | Incomplete insulation | Audits, LOTO, waste heat | Field validation and monitoring |
Technology to strengthen barriers
Digitalization adds value when it improves visibility into safety barriers. Safety barrier dashboards, digital permits, e-LOTO, mobile rounds, online monitoring, alarm analytics, Industrial Internet of Things (IIoT) sensors, digital twins, historians, and integrated action management can reduce the time between a deviation and a decision.
Digital maturity is not about having more applications, but about connecting critical process information. A PHA, an inspection, a silenced alarm, an SIS bypass, or a MOC action must be able to be linked to the equipment, the risk scenario, and the affected barrier. Without that traceability, the organization retains documents but loses visibility into the actual risk.
With this management approach, specialized platforms like AsInt enable the digitization process to be directed toward integrated risk management, asset integrity, and process safety. Their solutions integrate with workflows such as HAZOP, PHA, LOPA, SIL/SIF, and integrity analysis, helping to connect risk scenarios, critical equipment, affected barriers, and closure actions within a single traceable environment.
All new technology must undergo MOC. Changing control logic, a Human-Machine Interface (HMI), a network architecture, a historian, an alarm configuration, or remote access can alter process boundaries without physical intervention. The NIST Cybersecurity Framework 2.0 (NIST CSF 2.0), published in 2024, organizes cybersecurity outcomes to govern, identify, protect, detect, respond to, and recover from cyber risks.
All new technology must undergo MOC. Changing control logic, a Human-Machine Interface (HMI), a network architecture, a historian, an alarm configuration, or remote access can alter barriers without physical intervention in the process. The NIST Cybersecurity Framework 2.0 (NIST CSF 2.0), published in 2024, organizes cybersecurity outcomes to govern, identify, protect, detect, respond to, and recover from cyber risks.
Alarms, SIS, and Human Response
Alarms are human-dependent safeguards; they must be necessary, clear, actionable, and provided in a timely manner. ANSI/ISA-18.2-2016, Alarm Management for the Process Industries, establishes requirements and best practices for the alarm lifecycle: philosophy, identification, rationalization, design, operation, maintenance, monitoring, MOC, and auditing.
SISs require specific treatment. The IEC 61511 series, Functional Safety: Safety Instrumented Systems for the Process Industry Sector, covers the specification, design, installation, operation, and maintenance of SIS; the IEC 61511:2026 SER series compiles the current documents, including IEC 61511-1:2016+AMD1:2017.
An SIF is a specific function that brings or maintains the process in a safe state. The Safety Integrity Level (SIL) defines the level of risk reduction required for that SIF. This requires independence, periodic testing, functional competence, bypass management, change control, and analysis of actual demands.
Organizational culture and leadership
A safety culture is evident when an organization makes decisions based on risk. If a unit reduces its workload due to an unavailable critical barrier, if maintenance rejects non-conforming spare parts, if inspection requires evaluating an extension, and if operations reports deviations without fear, the system works.
CCPS defines process safety culture as the combination of group values and behaviors that determines how process safety is managed. In the field, this is seen in what is tolerated, corrected, escalated, or stopped.
Keys to strengthening accident prevention
Prevention improves when there is a living record of critical barriers by risk case. Each barrier must have an owner, function, acceptance requirement, verification frequency, failure condition, indicator, bypass rule, and compensatory action.
It is also necessary to periodically review high-consequence events, validate layer independence, audit operational discipline, close out overdue actions, and use early-warning metrics in operational meetings. The key question is not “Does the procedure exist?” but rather: Which barriers are degraded today, and what level of risk does the unit accept?
Conclusions
Process safety matures when barriers are managed as critical protective assets. Process risk is controlled through well-understood sequences, clear operating limits, asset integrity, reliable alarms, verified SIS, effective MOC, comprehensive PSSR, and sustained operational discipline.
Accident prevention depends on measuring the actual condition of barriers, closing out deviations, rationalizing alarms, controlling temporary changes, securing instrumented systems, and acting before multiple defenses degrade simultaneously. When decisions are based on technical evidence, the plant retains operational control and reduces the likelihood of major events.
Do you know how many of your critical barriers are degraded today?
References
- NIST Cybersecurity Framework 2.0. https://nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.29.pdf
- Vidyatec – Process Safety Management, Hazards, Barriers and Digitalization. https://vidyatec.com/blog/process-safety-management-101-hazards-barriers-and-digitalization/
- IEC 61511:2026 SER. https://webstore.iec.ch/en/publication/5527
Frequently Asked Questions (FAQs)
What are process safety barriers?
These are technical, instrumental, mechanical, administrative, or organizational controls that prevent, detect, control, or mitigate major incidents.
How is process risk managed?
Credible cases are identified, consequences are assessed, safeguards are assigned, and it is verified that they remain in place throughout the operation.
Why is operational discipline important?
Because many barriers depend on human decisions: respecting limits, responding to alarms, complying with permits, closing MOCs, and stopping unsafe activities.
What mistakes weaken the barriers?
Standardized bypasses, expired tests, ignored alarms, outdated procedures, incomplete MOCs, and startups without a closed PSSR.

